Анализ криптокошельков на риск и легальность транзакций
Следите за безопасностью своих переводов: проверяйте не только свой кошелёк, но и кошелёк отправителя, чтобы заранее выявить возможные риски

Связи миксеров

Доступ API

Сетевой анализ

Мониторинг риска

Поддержка сетей

Проверка кошелька
Comprehensive Cybersecurity Solutions for Modern Threats

Network Security

Cloud Security

Regulatory Compliance
Есть сомнения по поводу предыдущих транзакций?
Риски накапливаются незаметно и проявляются в самый неудобный момент
99.2%
Глубина проверки

AML-проверка криптокошелька — это не вопрос доверия, а вопрос предсказуемости. «Грязные» средства могут попасть на адрес случайно: через P2P, сдачу, airdrop или DEX. Проблемы возникают не сразу, но при выводе зачастую возникают заморозки, проверки, потеря времени и средств. Проверяя свой и чужой кошелёк заранее, и вы увидите риски до того, как они станут реальной проблемой.
Robust Cybersecurity Services for Today’s Threats


AML-проверки

Портфолио трекер


Возврат средств

KYT Office

Graph

AML-сертификация
Complete Cyber Defense Against Modern Attacks
Defending Businesses With Expertise And Innovation

Robust Cybersecurity Services for Today’s Threats
Protect your business from ever-evolving cyber risks with our end-to-end security solutions. We offer advanced threat detection, real-time monitoring, and proactive defense strategies tailored to your infrastructure. Whether you’re safeguarding sensitive data or ensuring compliance, our robust cybersecurity services help you stay secure, resilient, and ahead of the threat curve.

Customer Data Protection

Remote Workforce Protection
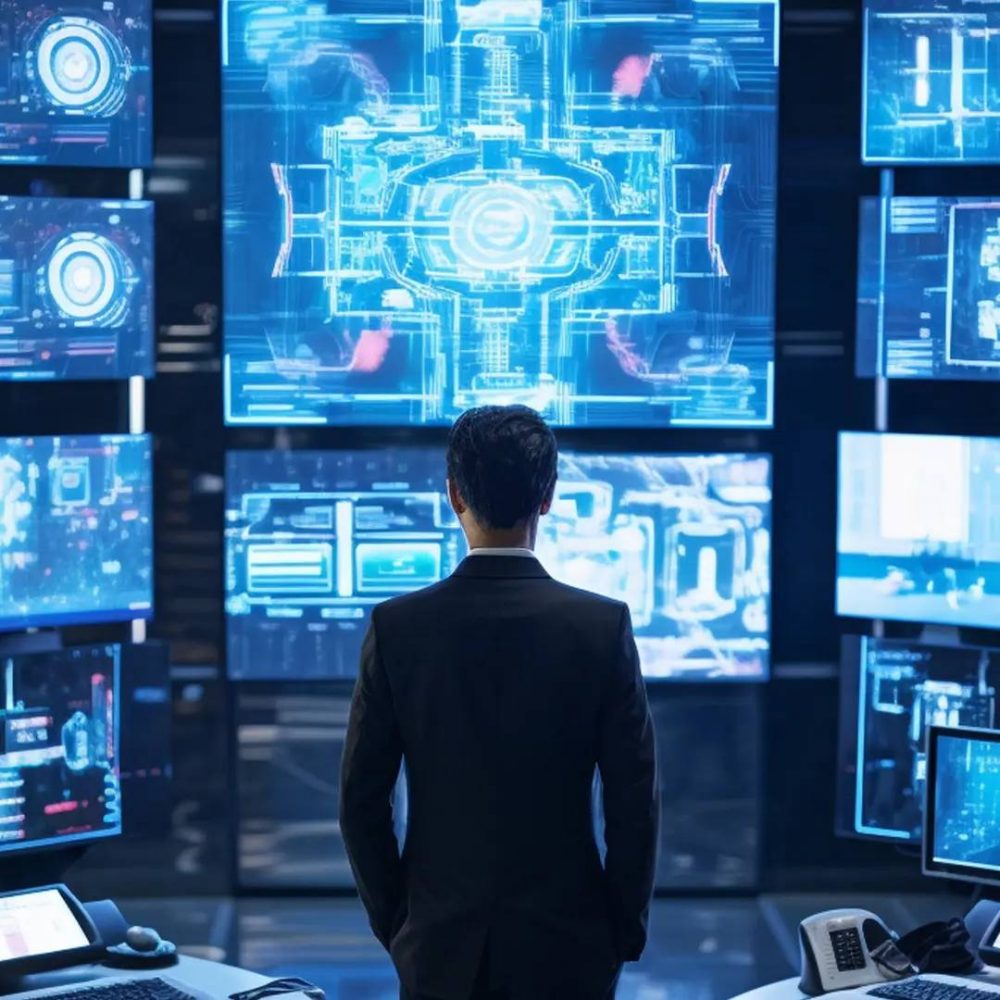
Real-Time Threat Detection
Hear It from Our Happy Customers
See how our cybersecurity solutions have helped businesses stay secure, compliant, and resilient against evolving digital threats.
Latest news and insights from our experts
Strengthen your network with advanced cyber security services designed to prevent attacks and safeguard your digital assets.
Need 24/7 Protection From Cyber Attacks?